- April 16, 2026
- 345 Views
- 1 Likes
- Automation & Integration, Digital Transformation, IT Optimization
Quantum Computing and Post-Quantum Security: Safeguarding Federal Systems for the Next Era
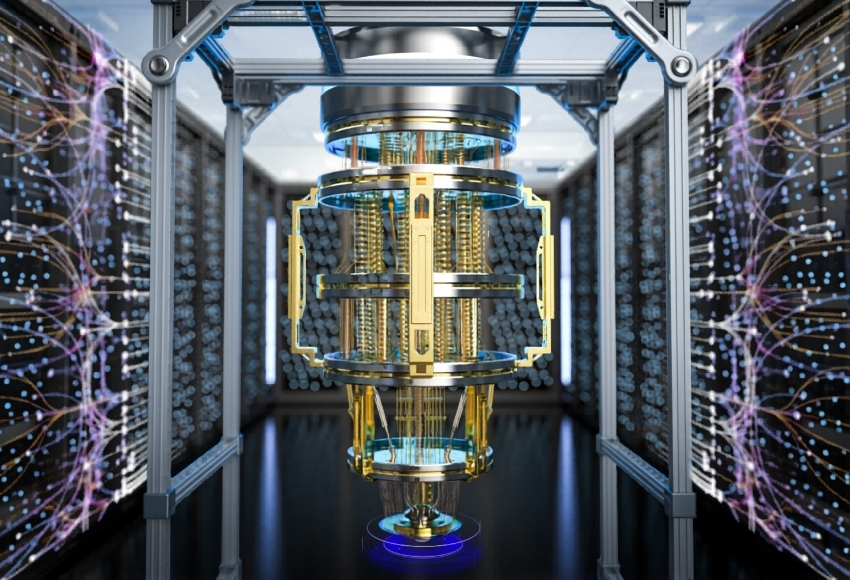
Quantum computing is poised to transform how federal and enterprise systems process, secure, and analyze data. Unlike classical bits that exist only as 0 or 1, quantum bits—qubits—can exist in multiple states simultaneously through superposition. When qubits interact through entanglement, they unlock computational possibilities far beyond classical architectures, enabling high-speed problem solving in areas such as logistics, drug discovery, and cryptographic analysis.
As promising as this sounds for innovation, the same power threatens the core of our digital trust model—modern encryption.
As promising as this sounds for innovation, the same power threatens the core of our digital trust model—modern encryption.
Security Threats and Compliance Imperatives
Current cryptographic standards (RSA, ECC) rely on mathematical problems that would take classical computers centuries to solve, yet quantum computers could break these in minutes. This introduces two converging threats:
- Harvest Now, Decrypt Later: Adversaries may already be collecting encrypted federal and contractor data—intending to decrypt it once quantum capabilities mature.
- AI Data Compromise: Once decrypted, sensitive training data can be reverse-engineered, corrupting AI outputs and undermining models used in defense, cybersecurity, and healthcare algorithms.
NIST Post-Quantum Standards and Federal Readiness
In response, the National Institute of Standards and Technology (NIST) finalized the first three Post-Quantum Cryptography (PQC) standards in 2024. These algorithms are designed to resist both classical and quantum-based attacks and will gradually become mandatory within federal environments—including agencies, DoD contractors, and systems subject to NSA CNSA 2.0 requirements.
Organizations will need to take proactive steps now to ensure alignment with emerging federal and cybersecurity mandates:
Organizations will need to take proactive steps now to ensure alignment with emerging federal and cybersecurity mandates:
- Initiate Quantum-Safe Inventory Assessments: Identify encryption dependencies across IT infrastructure, cloud workloads, and IoT endpoints.
- Develop a PQC Migration Roadmap: Begin introducing NIST-approved hybrid encryption—to layer classical and quantum-resilient algorithms until full transition is required.
- Reassess Zero-Trust Architecture: Integrate PQC-ready identity and signature schemes into authentication and authorization workflows.
- Strengthen Vendor and Supply Chain Oversight: Require compliance verification for subcontractors and technology vendors under government contracts.
- Update AI Governance: Evaluate training pipelines and data integrity measures to prevent exposure from pre-quantum encrypted datasets.
Application Beyond Cybersecurity: The Innovation Edge
Beyond defense and data protection, quantum computing offers profound productivity advantages for federally funded research and innovation:
Drug Discovery Acceleration through molecular simulation at atomic precision.
Genomic Analysis across massive datasets to identify rare gene expressions.
Clinical Trial Optimization and adaptive design modeling.
Supply Chain and Energy Modeling for DoE, NIH, and DoD research collaborations.
The challenge—and opportunity—lies in balancing these scientific gains with robust quantum-resilient security architecture that safeguards research data and IP against next-generation threats.
The challenge—and opportunity—lies in balancing these scientific gains with robust quantum-resilient security architecture that safeguards research data and IP against next-generation threats.
Charting Your Post-Quantum Path
Transitioning to quantum-safe infrastructure isn’t a single technology upgrade—it’s a strategic modernization effort that affects encryption, identity management, data lifecycle, and compliance posture across your entire ecosystem.
Bithrive helps federal agencies and contractors prepare for this transition through tailored modernization services that address both technical and regulatory readiness:Cloud Security Modernization – Upgrading hybrid and multi-cloud environments to integrate post-quantum cryptography (PQC) without disrupting ongoing missions or workloads.
Compliance and Readiness Assessments – Aligning architectures with NIST PQC, FedRAMP, and CMMC frameworks while documenting evidence for federal audits and procurement.
Secure Data Migration – Implementing encryption lifecycle management that protects sensitive data throughout storage, transport, and AI model training processes.
Architecture and Integration Design – Engineering Quantum-Resilient Architectures (QRA) that combine classical and hybrid cryptography to future-proof applications and APIs.
Consulting and Workforce Enablement – Guiding CIOs, CISOs, and technical teams through awareness and training programs focused on measurable quantum readiness milestones.
Through these initiatives, Bithrive enables federal and enterprise clients to modernize securely, meet emerging standards, and preserve operational trust amid shifting cybersecurity paradigms.
The quantum transition is already underway—organizations that act now will protect critical assets while gaining competitive advantage in secure innovation.
Sources:Gartner Predicts 2026: Post-Quantum Cybersecurity
PRNewswire: The $15 Billion Post-Quantum Migration and NIST Standards
Google Research: Preparing for Quantum Attacks on ECDSA
Bithrive helps federal agencies and contractors prepare for this transition through tailored modernization services that address both technical and regulatory readiness:
Through these initiatives, Bithrive enables federal and enterprise clients to modernize securely, meet emerging standards, and preserve operational trust amid shifting cybersecurity paradigms.
The quantum transition is already underway—organizations that act now will protect critical assets while gaining competitive advantage in secure innovation.
Sources:


